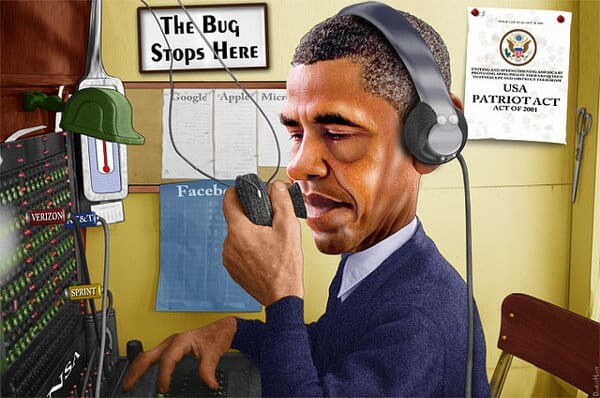
Time to stop this theatre of the absurd. WebRTC isn’t going to save us from government scrutiny.
I am not sure about you, but I have this déjà vu from this weekend. Since the leak about the NSA getting data streams from various US companies, the web is running amok. And somehow, WebRTC guys are trying to ride this wave. To where? Who knows.
But let me first explain.
I’ve been in this industry for over a decade. Video conferencing uptake was dismal at best. Yes, enterprises adopted it, but somehow the whole industry when you looked at it wasn’t big. What do you do when that happens? You try to make people adopt it.
And with video conferencing, I’ve seen several iterations:
- Planes get crashed into buildings? Try to promote video conferencing over business trips
- Gas prices rise? Try to promote video conferencing over business trips
- A volcano eruption disrupts international flights? Try to promote video conferencing over business trips
Can you notice a pattern?
And now it seems that whenever there’s talk about privacy and security, people start promoting WebRTC as the savior. I’ll be the first to say security of WebRTC is top notch, but from that to solving humanity’s problems?
Just search social networks for WebRTC and security and see the amount of chatter in those echo chambers.
Yes, WebRTC does P2P for the media and enables encryption. But no – it is only a technology and how vendors will be using is what really matters. And there, I see more systems that will end up passing media through a server than not – just because it opens up more features and capabilities.
I had the opportunity to read Thomas Frey’s article about the end of theft this past week. It got me into thinking of many things, but coupled with what we see now, I think we can start debating about privacy – and the end of privacy. When everything gets connected, and when our own devices are always on, always listening to our voice commands and always watching us for our needs – where does WebRTC even play a role?
With this hyper connectedness comes the relinquishing of privacy. And it won’t be all bad mind you – it is also why two months ago I warmly suggested Ramez Naam’s science fiction book: Nexus.
–
Security is important. Privacy is as well. Governments not violating these rights and even promoting them is important. But from that to saying WebRTC is the solution?
We’re better than that. WebRTC has a lot of advantages, but I wouldn’t say that maintaining our privacy against governments and the powers that be is one of them.
And frankly, I don’t think WebRTC needs to be promoted that way to be successful.
–
I wouldn’t have burdened you with a post this weekend, but my G+ notifications were too much to bear without sharing.
Have a great weekend!

I agree that the hype over webRTC is excessive and probably counter productive.
However there are a couple of areas where it differs from traditional videoconferencing.
1) Video conferencing never took off because the user experience was terrible, it was overpriced and almost never worked without at least 2 geeks at each end. Don’t blame hype for it’s failure.
In contrast there is no user experience in webRTC, it is whatever the web designers wish it to be.
Some will be terrible, but many will be good, diversity allows winners to flourish.
2) Both the current main webRTC implementations are opensource. If you are a journalist, lawyer, aid worker or any of the other folks who need private conversations, you can download an independently built and verified version of chrome or firefox, which has been checked at the source level for backdoors.
This is different from the video conferencing case, where proprietary closed source code was used and encryption was optional if available at all.
3) WebRTC makes it easy to run your own webRTC service. Meaning that you don’t have to depend on the privacy policies of a vendor or service provider, if you have a php enabled website, you can just put the open source apprtc code on it and you have your own secure video conference service.
Finally, before you take the Scott McNealy ‘privacy is dead, get over it’ line, go talk to a Russian or East German grandmother. Or watch the film ‘The lives of others’.
All true Tim.
I just think that in the end of the day, people will end up using powerful WebRTC based services, those that archive calls, provide transcipts of them automatically and make them searchable. In such a case, where is that privacy we speak about in WebRTC?
Remember that WebRTC isn’t technically different than a SIP profile in how you see it in the network. Yes, it is easier for developers to use, and that makes it disruptive – but it won’t end up being more secure than anything else for the majority of the people.
Totally agree. It is not a technology issue, it is a policy issue.
Skype is probably the greatest P2P network in the world and the NSA has access to that. Not sure exactly in what form, but I am guessing that they would be able to eavesdrop on any Skype conversation if they ask for it.
I think the biggest issue here isn’t that WebRTC will, by itself, save anyone from intrusions on their privacy. What’s key, and you touched on this in your post on WebRTC security, is that we’re going out of our way to provide the tools that will allow services to prevent such intrusions. If a service wants to send your media through a server so it can log conversations for your later perusal, that’s something the architecture lets them do — with the implicit agreement between the service provider and their users that they have access to those conversations.
Where WebRTC differs from the other technologies you cite is that it incorporates tools for services to demonstrate to users that they do *not* have access to the communications, and services can easily tout that as a selling point. Is Hangouts going to use those tools? Is Facebook? Probably not. But I would be shocked if we didn’t see hundreds, if not thousands, of small services popping up, based on WebRTC technology, that do make use of these tools — because they’re baked into the browser, and (unless we really botch this) trivial to make use of.
It’s not a panacea, but this ease of use certainly shows more promise for keeping communications away from prying eyes — those of your own government, a foreign government, or a malicious network operator — than any of its predecessor technologies.
WebRTC depends on browser implenetation, if browser vendor works together with NSA, let’s take Google as an example, it means that p2p encryption and security means nothing, since you have trojan horse on your computer in form of browser and it can send stream wherever is required. But hopefully it’s just won’t happen 😉
Alexey. As I pointed out earlier, chrome is open source so you can see such backdoors if you know what to look for.
If you don’t there are independently compiled versions that you can download from sites you trust more than Google.
Tsahi, on the wire, webRTC is different from SIP. The mandated DTLS-SRTP encryption does not exchange keys over a signalling channel. By contrast most SIP/RTP traffic isn’t encrypted at all.
Of course WebRTC isn’t unbreakable or immune to interception, but it is designed to be a significantly harder nut to crack.
Hi there,
I’m quite a noob when it comes to computer science but when the whole spying mechanisms of our governments got public in the last days I thought WebRTC probably is not better than Skype… It would be nice if some of the more skilled people here could deny or confirm my thought.
The reason I’m thinking this is that as far as I know Skype also uses good encryption. However we now know nearly for sure that Microsoft has backdoors implemented that allows “authorized people” to avoid these encryption.
WebRTC in Chrome is maintained by Google and we have no way to check if the Google Chrome Browser is compiled with the WebRTC implementation as Google says us it is. So couldn’t it be that they also implement some kind of “master certificate” with which an institution or anyone whit this certificate is able do decrypt any WebRTC media stream he sniffs (from a transatlantic fiber optic cable or any other source)…?
Anything is possible.
However there are 3 factors that make it difficult for such a “master certificate” to be embedded in WebRTC.
1) Public specification by the IETF: The webRTC media format is well documented in RFCs. Experts have inspected the protocol design and presumably someone would comment if there was a major flaw.
2) Multiple implementations: Google aren’t the only folks to build a webRTC implementation. With the release of firefox 22 there are now 2 browsers that implement the spec. There are also some server side implementations (e.g. ours on phono.com ) . It is unlikely that all the implementations have the same well hidden backdoor.
3) Open source: Both Chrome and Firefox are opensource, if you care to you can download the source code, inspect it and build your own browser. If you did find a ‘master certificate’ or other back door, you could remove it. The cryptography we used in the phono.com implementation is also opensource.
While true, I think the main issue here Tim is the understanding that the moment your service becomes large enough, there’s no guarantees that a government or anyone else with vested interest won’t scrutinize it closely. With governments the problem is that they can force their way into the service and record/see whatever they wish there – no matter the protocol or the technology.
Rinko, you are correct. The issue isn’t the spec or the level of encryption but rather the way companies implement their service on top of it.