It's security.
As I prepare for another workshop that I am giving next week about WebRTC screen sharing, I decided to refresh another set of my slides - something I do for every workshop.
This time, I took a look at the ones I present on the permissions mechanism built into WebRTC in Chrome. It now looks something like this:
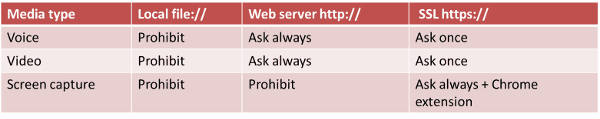
- Local files can't access anything - that's so you won't get bit by viruses and scams sent over email as files
- HTTP requires permission each time to access the camera and the microphone
- HTTPS requires permission only once - the difference between the two may be security, but it also relates to Google's current foray at HTTPS Everywhere
- And screencasting? That is only enabled through a Chrome extension
Why that Chrome extension for screencasting?
Because giving access to the screen is far more dangerous than letting someone see you pick your nose. And it doesn't light green on your webcam when it does either. Oh - and that same code that enabled screen casting? It also controls what's on that screen since it is running in the browser.
If you want the gory details, then check out this research paper from Carnegie Mellon University (pdf). The title? All Your Screens are Belong to Us:
Attacks Exploiting the HTML5 Screen Sharing API
How does an extension helps us then? By forcing these to live inside Chrome extensions, Google are becoming the gatekeeper. Extensions for Chrome can only be delivered through the Chrome Web Store. This allows Google to maintain some form of governance, along with the ability to throw away extensions that are considered malware if they see fit. It might not catch everything before it gets into the store, but once found - it gets eradicated.
WebRTC offers security when screencasting
Consider this another layer of security that WebRTC offers, along with the fact that the code of the extension itself is wide open.
Now ask yourselves - would you prefer downloading and running a collaboration service that has access to anything and everything on your machine at all times coming from a no-name startup (or a company with questionable origins) - or would you rather just use something with far less exposure and the same functionality? One that will even get disabled if it doesn't play by the rules.
And people still argue with me when I say that WebRTC is the most secure VoIP technology.

